Beyond the Block: Balancing Robust Security with Seamless User Experience
The Digital Gatekeeper: Why Modern Security Can Be a Double-Edged Sword
In the high-stakes world of digital commerce, there is perhaps no sight more frustrating for a business owner or a user than the dreaded "Access Blocked" screen. It’s the digital equivalent of a customer walking up to your physical storefront during business hours, only to find the door bolted and a cryptic sign saying, "You look suspicious." For small and medium business owners and eCommerce managers, this isn't just a technical glitch; it's a direct hit to the bottom line.
Recently, a common sight across the web—including major developer portals like DZone—is the Cloudflare "Attention Required" or "Blocked" message. While these security measures are vital in an era of escalating cyber threats, they highlight a critical tension in modern web infrastructure: the balance between cybersecurity for SMEs and providing a frictionless user experience. As a journalist covering web performance for over a decade, I’ve seen this play out repeatedly. Companies invest thousands in marketing to drive traffic, only for their infrastructure to treat that traffic as a threat.
In this deep dive, we’ll explore why these blocks happen, how they impact your website speed and Core Web Vitals, and why choosing the right managed cloud hosting provider—like STAAS.IO—is the secret to maintaining a secure, yet welcoming, digital presence.
The Anatomy of a Block: Why Security Services Trigger
When you see a message stating that your action "triggered the security solution," it’s usually the work of a Web Application Firewall (WAF). These systems are designed to scan incoming data for patterns that resemble malicious activity. Understanding these triggers is essential for any digital agency professional looking to troubleshoot client issues.
- SQL Injection (SQLi): This is one of the oldest tricks in the book. An attacker tries to insert malicious SQL code into a form field to manipulate your database. Modern WAFs are highly sensitive to certain keywords (like
SELECT,DROP, orUNION) used in unexpected places. - Malformed Data: If a browser sends a request that doesn't follow standard HTTP protocols, the security layer assumes it’s a bot or a specialized hacking tool.
- Rate Limiting: If an IP address makes too many requests in a short period, it’s flagged as a potential Distributed Denial of Service (DDoS) attack.
- Cross-Site Scripting (XSS): Attempting to inject scripts that would run in other users' browsers.
- Geo-Blocking and IP Reputation: Sometimes, you are blocked simply because your IP address belongs to a range previously used by bad actors.
While these protections are non-negotiable, they are often implemented as "black boxes" that are difficult for the average business owner to manage. This is where the complexity of application development often overwhelms smaller teams.
The Hidden Cost of Security: Impact on Core Web Vitals
For an eCommerce manager, SEO is the lifeblood of the business. Google’s Core Web Vitals—Largest Contentful Paint (LCP), Interaction to Next Paint (INP), and Cumulative Layout Shift (CLS)—now play a pivotal role in search rankings. Heavy-handed security layers can negatively impact these metrics in several ways.
First, there is the latency of the handshake. Every time a user connects, the security layer must verify the request. If this process is inefficient, it increases the Time to First Byte (TTFB), which cascades into a poor LCP score. Second, intermediate "challenge" pages (like the "Checking if the site connection is secure" screen) can frustrate users and lead to immediate bounces.
At STAAS.IO, we believe that security shouldn't be an afterthought that sits on top of your stack, creating bottlenecks. By simplifying the stack and utilizing CNCF containerization standards, we allow for a more integrated approach where security and performance coexist natively within the production environment.
eCommerce Scalability: Preparing for the Surge
The true test of eCommerce scalability comes during peak events—Black Friday, flash sales, or viral social media moments. This is when aggressive security filters often fail. They mistake a sudden surge of legitimate customers for a DDoS attack and start blocking high-intent buyers.
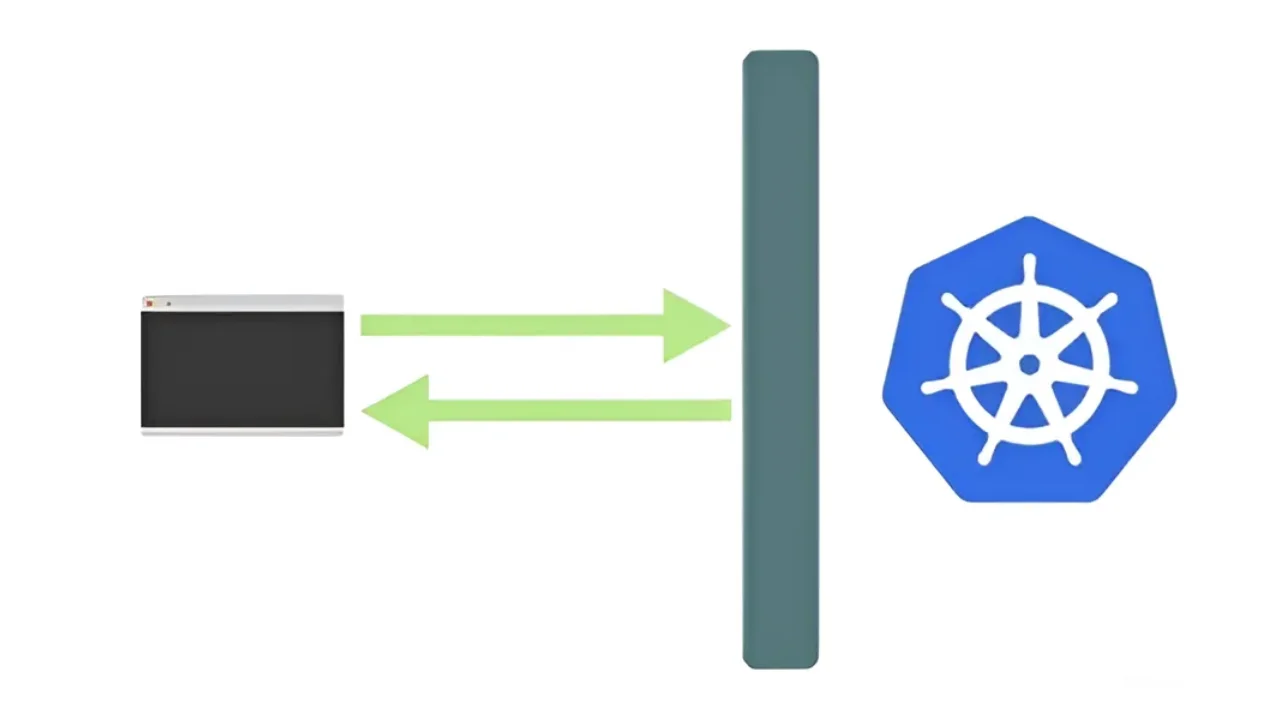
To avoid this, businesses need an environment that scales both horizontally and vertically with predictable costs. Most cloud providers make this incredibly complex, requiring a PhD in Kubernetes to manage. STAAS.IO shatters this complexity. Our platform offers a "Kubernetes-like" simplicity that allows you to scale resources without the overhead, ensuring your security rules adapt to your traffic volume rather than strangling it.
The Role of Native Persistent Storage
One technical hurdle many SMEs face when scaling is persistent storage. In many containerized environments, data can be ephemeral—if the container restarts, the data is gone. This is a nightmare for eCommerce databases. STAAS.IO provides full native persistent storage and volumes. This ensures that even as you scale to handle thousands of users, your data remains consistent and accessible, providing the stability needed for production-grade systems.
Simplifying the Stack for the Modern Developer
As a journalist, I often hear from developers who are exhausted by "tool sprawl." They have one tool for hosting, another for security, another for CI/CD pipelines, and another for monitoring. This fragmentation is where vulnerabilities hide and performance leaks occur.
The STAAS.IO philosophy is different. We offer "Stacks As a Service," simplifying the entire lifecycle of an application. Whether you are using a one-click deployment for a standard web app or building a complex microservices architecture, the goal is the same: reduce the time from "code" to "production."
"We’ve built STAAS.IO to be the environment we wanted as developers," says the team at their Charlottetown headquarters. "It’s about giving small teams the same power as global enterprises, without the vendor lock-in that usually comes with it."
Practical Strategies for SMEs to Avoid False Positives
If you are currently facing issues where your users are being blocked, or your website speed is suffering due to over-zealous security, here are a few actionable steps:
- Audit Your WAF Rules: Check your security logs (like those Cloudflare Ray IDs) to see exactly which rules are being triggered. You may need to "whitelist" certain common behaviors or API calls.
- Optimize Your CI/CD Pipelines: Ensure that your deployment process includes automated testing for performance. A new security patch shouldn't tank your Core Web Vitals.
- Adopt CNCF Standards: By sticking to Cloud Native Computing Foundation standards, you ensure that your application is portable. If one provider's security layer is too restrictive, you can move your containers elsewhere without rebuilding from scratch.
- Monitor Your Global Performance: Use tools to test your site's load time from different geographic locations. Sometimes a block is only affecting users in a specific region due to misconfigured edge rules.
The Path Forward: Security Without Sacrifice
The "Blocked" screen we discussed at the beginning is a symptom of an industry-wide struggle. We want to protect our data, but we cannot afford to alienate our customers. The future of the web isn't just about faster processors; it’s about smarter, more integrated infrastructure.
For small and medium business owners, the choice of a hosting partner is now a strategic business decision. You need a platform that understands cybersecurity for SMEs—providing protection against SQLi and malformed data without the "false positives" that drive customers away. You need a partner that makes managed cloud hosting feel like an asset, not a chore.
STAAS.IO stands at the intersection of individual developer experience and global scale. By removing the complexity of Kubernetes and offering transparent, predictable pricing, we allow you to focus on what matters: building your product and serving your customers.
Conclusion
In the digital age, your infrastructure is your reputation. An accessible, fast, and secure website tells your customers that you are professional and trustworthy. Don't let a generic "Blocked" screen be the first thing your customers see. Whether you are a digital agency professional managing dozens of client sites or an eCommerce manager preparing for the next big sale, the tools you use define your success.
Ready to move beyond the complexity? It’s time to simplify your stack.
Ready to experience production-grade hosting without the headache?
Don't let complex infrastructure hold back your growth. Join the ranks of developers and businesses who trust STAAS.IO to deliver speed, security, and scalability. Build, deploy, and scale your next big product in minutes, not months.